Wireless Lan Client Configuration Guide For Mac
Iii Cisco Aironet Wireless LAN Client Adapters Installation and Configuration Guide for Mac OS OL-1377-03 CONTENTS Preface ix Audience x Purpose x Organization x Conventions xi Related Publications xii.
The setup assistant guides you through the initial configuration options of your client adapter and network settings. Each screen contains descriptive information to assist you in configuring your client adapter. Note You can click underlined words or blue colored words on the setup assistant screens to obtain additional descriptive information. You can also click the Back button to return to a previous screen. Follow the steps below to complete the initial configuration settings for your wireless system: Step 1 If the Introduction screen is not visible, click the Introduction tab (see ). Figure 3-3 Setup Assistant Introduction Screen Step 2 Read the screen information and click Start to continue to the Client Name screen. Note Click the Done button (on any screen) to exit the setup assistant and to manually configure your client adapter using the Aironet Client Utility.
About the author: Robbie Harrell (CCIE#3873) is the National Practice Lead for Advanced Infrastructure Solutions for SBC Communications. He has more than 10 years of experience providing strategic, business and technical consulting services. Robbie lives in Atlanta and is a graduate of Clemson University.
Click the up and down arrows next to the Network Type field and perform one of the following operations: • If your computer connects to an access point, select Computer to Access Point. Click Next to continue to the Power screen. • If your computer connects to another computer in a peer-to-peer (ad hoc) network, select Computer to Computer. Then click the up and down arrows next to the Channel field and select the operating frequency channel for the computers on your network. Click Next to continue to the Power screen.
Step 2 Select Control Panels > TCP/IP. The TCP/IP window appears. Step 3 Select Cisco Wireless LAN Adapter in the Connect via drop-down box.
Administrators can control access using,. MAC-based Access Control MAC-based access control admits or denies wireless association based on the connecting device’s MAC address. When a wireless device attempts to associate, the Meraki AP queries a customer-premise RADIUS server with an Access-Request message. The RADIUS server can admit or deny the device based on the MAC address, responding to the Meraki AP with either an Access- Accept message or an Access-Reject message, respectively. This authentication method requires no client-side configuration.
Caution Do not force or rock the adapter into the expansion slot as this could damage the adapter and the slot. If the adapter does not insert easily, remove the adapter and reinsert it. Step 7 Replace the computer cover. Step 8 Attach the 2-dBi antenna to the adapter's antenna connector until it is finger-tight.
• If you are not connected to a DHCP or BootP server, select Manually in the Configure drop-down box and enter the client adapter IP address, the subnet mask, and the router IP address. If required by your wireless network, enter the IP addresses for the domain name servers (obtained from your system administrator). Step 20 Click Apply Now to apply your TCP/IP configuration options. Step 21 Click System Prefs on the main menu bar and click Quit System Prefs.
Step 2 Click System Preferences. The System Preferences window appears. Step 3 Click the Network icon. The Network window appears. Note If a New Port Detected screen appears, click OK to activate the new port, such as Ethernet Adapter (en1) or PCI Ethernet Slot 1. Step 4 Click the Location up or down arrows and select a location.
The Access points each interface with the identity source at time of the client association. Below are the identiity sources that can be used with WPA2-Enterprise. • Meraki RADIUS - Cloud Hosted • Network-wide Users can connect and login with PEAP and EAP-TTLS • WiFi Security configures endpoint devices to connect with • - Customer Hosted • Cisco Identity Services Engine (ISE) • FreeRADIUS • Juniper Steel-Belted RADIUS or UAC • ForeScout CounterACT • Aruba Clearpass • • • •.
Describes the most common buttons.
During monitoring, a window shows that monitoring is in progress. Monitoring continues as long as this window is open and you're on the same Wi-Fi network, even when your Mac is asleep. If Wireless Diagnostics finds an issue, it stops monitoring and shows a brief description of the issue.
For example, due to real time application constraints, voiceover Wi-Fi traffic needs a higher priority than Safari web traffic. Various standards exist to help network devices agree on how different types of traffic are marked to make sure they are prioritized. QoS Fastlane greatly simplifies this agreement process so that network congestion is minimized and time sensitive traffic (like voice or video) is delivered on time. To choose which iOS apps have their traffic prioritized by QoS Fastlane, you must configure the network with a configuration profile.
This configuration still grants the option of FT to iOS clients. IOS devices and Cisco APs mutually signal that adaptive 802.11r is supported by the network and that FT can be used. Legacy wireless clients that don’t support 802.11r can still join the same network but won’t benefit from faster FT roaming. Wireless application traffic in enterprise environments often needs to be prioritized by its type.
Windows software will walk you through the setup and configuration of the WLAN card, but I can attest from experience that it is really confusing. In addition, if you have to modify these settings, it can be very cumbersome.
Caution Do not force the PC card into your computer's PC card slot. Forcing it will damage both the card and the slot. If the PC card does not insert easily, remove the card and reinsert it. Step 2 Hold the PC card with the Cisco logo facing up and insert it into the PC card slot, applying just enough pressure to make sure it is fully seated (see ). The PC card slot is usually on the side of the computer, depending on the model. Figure 3-4 Inserting a PC Card into a Computing Device Note You can remove and reinsert your PC card when necessary. Refer to the for instructions.
You can then resume monitoring or continue to the summary for details and recommendations. Wireless Diagnostics automatically saves a diagnostics report before it displays its summary. You can create the same report at any time by holding down the Option key and choosing Create Diagnostics Report from the Wi-Fi status menu. It can take your Mac several minutes to create the report. • macOS Sierra saves the report to the /var/tmp folder of your startup drive, then opens that folder for you.
Then double-click Aironet Client Utility on the Applications screen. Or, click the Aironet icon on the Mac OS X menu bar and select Open the Aironet Client Utility. If the Aironet Client Utility icon is not on the Applications screen or the client utility screen does not appear, verify that your Macintosh is running Mac OS X and reinstall the client utility and driver. If you continue to have problems, refer to the. Step 2 When the client utility screen appears, check the status line on the bottom of the screen. The status line should indicate that the radio is associated to an access point, the access point name, and the IP address.
802.11r offers wireless clients the ability to quickly roam between APs on the same network. Fast Basic Service Set Transition (FT) allows clients to roam between APs without taking the time to re-authenticate to each new AP. Adaptive 802.11r allows you to set up a network without choosing Enable for Fast Transition.
WPA2-Enterprise with 802.1X Authentication 802.1X is an IEEE standard framework for encrypting and authenticating a user who is trying to associate to a wired or wireless network. WPA-Enterprise uses TKIP with RC4 encryption, while WPA2-Enterprise adds AES encryption.
If there is a symbol beside the network name that looks like a lock, it means the AP is configured with security mechanisms and you will have to get this information from the AP administrator to connect. Once connected (the GUI will show that you are connected) you can ascertain whether or not you have been assigned an IP address by doing the following: • Click on 'start' • Click on 'run' • In the command line, type 'cmd' to pull up a DOS window • In the DOS window, type 'ipconfig' • If you have been assigned the appropriate IP Addressing information, you will see something similar to the following: Microsoft Windows XP [Version 5.1.2600] (C) Copyright 1985-2001 Microsoft Corp. C: Documents and Settings Robbie Harrell>ipconfig Windows IP Configuration Ethernet adapter Wireless Network Connection 3: Connection-specific DNS Suffix.: IP Address......: 192.168.0.2 Subnet Mask......: 255.255.255.0 Default Gateway.....: 192.168.0.1 • • Make sure the information is applied to the wireless network connection. This is really straightforward. However, many new laptops are shipping with Intel Centrino Mobile network adapters already installed in the laptop. This means that you did not install a WLAN card, it was just there. The only way to configure the embedded WLAN card is via the Windows software installed on your PC.
Step 13 If the Almost There screen appears, this indicates your client adapter is associated to an access point but is unable to pass data through the access point. Perform one of the following operations: a. Click Finish to exit the setup assistant and use the client utility to help resolve the problem. Click Return to Setup Assistant to revise your settings using the setup assistant. Step 14 If the Troubleshoot screen appears, this indicates your client adapter is unable to associate to an access point. The screen status information identifies the problem area. Perform one of the following operations: a.
After the adapter is found, the Cisco pcm340 - Basic Properties window appears. Step 4 Under Radio, make sure that radio status is on. If it is off, click the Turn radio on button.
Basic Configuration on Mac OS 9 Basic configuration for Mac OS 9 has the following tasks: 1. Configure AppleTalk or TCP/IP 2. Configure the client adapter Configuring AppleTalk Configure AppleTalk only if you use the client adapter for an AppleTalk connection. To configure the computer to use AppleTalk, perform the following steps: Step 1 Click the apple-shaped icon in the top left corner of the desktop. Step 2 Select Control Panels > AppleTalk. The AppleTalk window appears.
You will need the laptop model number to do this, and I recommend this path to ensure that the drivers are compatible. Installing the GUI and knowing how to validate and configure the SSID, channel, security and IP address settings will solve 99% of the client issues associated with WLAN connectivity. Most of the other issues are related to performance of the environment and the back-end infrastructure supporting the WLAN network, all of which cannot be addressed by the end user.
Benefits of automatically renewing your license include: • Uninterrupted protection — Your subscription will continue with continuous protection • Worry free, peace of mind that your devices are always secure • Saves you time — We take care of everything for you and will send you notifications to inform you of your next billing date & confirmation that your license has been renewed • Flexibility — You may unsubscribe from this service at any time. 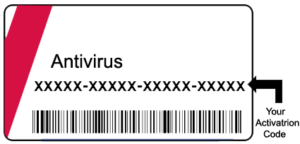 Auto-Renewal Plan Our hassle-free is designed to save you time, effort and risk by extending your subscription automatically before it expires*.
Auto-Renewal Plan Our hassle-free is designed to save you time, effort and risk by extending your subscription automatically before it expires*.
If the configuration options are not correct, click Cancel and go to. Click Quit to exit the setup assistant and to manually configure your client adapter using the Aironet Client Utility. Step 11 When a drop-down screen appears stating that your settings have been saved, read the information and perform one of the following steps: a. If you previously selected the Enable WEP option, click the Hexadecimal or ASCII check box and enter your WEP key in the entry box. If you previously selected the Enable LEAP option, enter your LEAP username and password in the entry boxes. A screen drops down to indicate your client adapter is being configured and trying to associate to an access point. When the test process completes, one of four screens will appear: • Congratulations • Almost There • Troubleshoot screen • Done The screens provide the following status information: • Saving of configuration settings—indicates whether your settings have been successfully saved in the preferences file.
The bottom edge of the adapter is the connector you will insert into the PCI expansion slot. Step 5 Tilt the adapter to allow the antenna connector and LEDs to slip through the opening in the computer back panel. Step 6 Press the client adapter into the empty PCI expansion slot until the adapter is firmly seated.
To help minimize cell overlaps, you should strive to use the lowest power setting that supports full coverage of your wireless cell. Click Next to continue to the Security screen. Step 8 Read the Security screen information on wireless network security options. If your wireless network uses these security options, click the Enable WEP or Enable LEAP check boxes. Note For computer-to-access point configurations, you must check with your corporate or enterprise network administrator for the appropriate security settings.
As a result, the card has a better chance of maintaining the radio frequency (RF) connection in areas of interference. The antenna is housed within the section of the card that hangs out of the PC card slot when the card is installed. • LM cards are shipped without an antenna; however, an antenna can be connected through the card's external connector.
His background includes positions as a Principal Architect at International Network Services, Lucent, Frontway and Callisma. Next Steps Helpful steps in WLAN: Analyzers and Browse.
The MR supports a wide variety of encryption and authentication methods— from simple, open access to WPA2-Enterprise with 802.1x authentication. Encryption and authentication are configured in the MCC under the Configure tab on the Access Control page. Generally speaking, the encryption method is configured under “Association requirements”, while the authentication method is configured under “Network sign-on method”.